Understanding the Insider Threat Landscape
Insider threats represent a significant vulnerability for organizations of all sizes. These originate from individuals who have authorized access to an organization’s systems, data, or physical premises, and who then misuse that access to harm the organization. This harm can manifest in various ways, including data theft, intellectual property espionage, sabotage, or financial fraud. Unlike external threats, which often involve sophisticated cyberattacks, insider threats leverage existing legitimate access, making them particularly difficult to detect through traditional perimeter security measures.
Categories of Insider Threats
Insider threats are typically categorized into two main groups:
- Malicious Insiders: These individuals intentionally seek to harm the organization. Their motives can be diverse, ranging from financial gain or revenge to ideological differences or dissatisfaction with employment conditions. They actively exploit their access for illicit purposes.
- Negligent Insiders: These individuals unintentionally compromise security due to carelessness, lack of awareness, or human error. Examples include falling for phishing scams, misconfiguring systems, or inadvertently sharing sensitive information. While their actions are not malicious, the consequences can be equally damaging.
The Evolving Nature of Insider Risk
The proliferation of digital data, cloud computing, and remote work arrangements has expanded the attack surface for insider threats. Employees often access sensitive information from various devices and locations, creating new avenues for data exfiltration or compromise. Furthermore, the increasing complexity of IT environments can obscure potentially malicious activities, making timely detection challenging. Organizations must recognize that insider threat is not a static problem but an evolving dynamic requiring continuous adaptation of defense strategies.
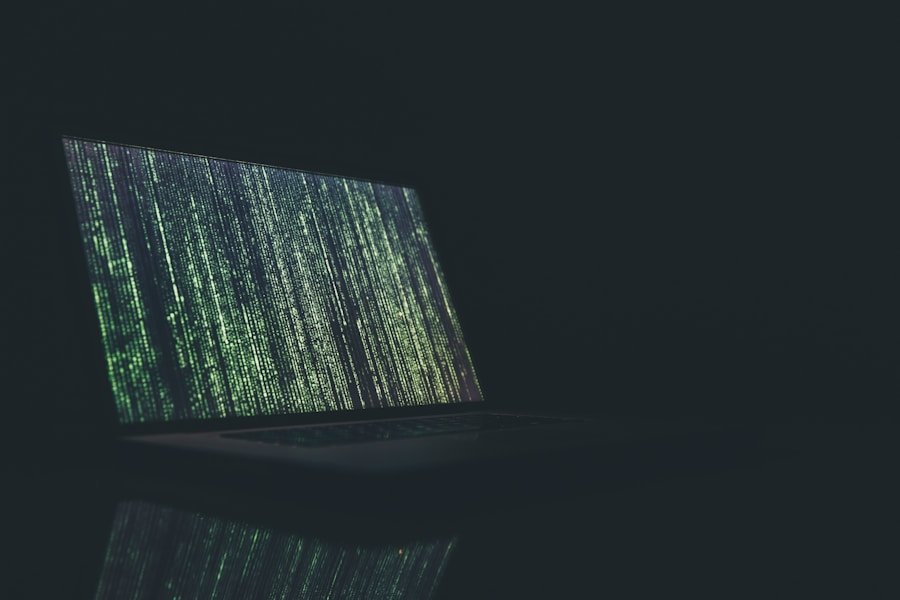
The Role of AI in Insider Threat Detection
Artificial intelligence (AI) offers a powerful suite of tools for enhancing insider threat detection. Traditional security systems often rely on predefined rules and signatures to identify suspicious activities. This approach can be effective against known threats but struggles to detect novel or evolving insider behaviors. AI, particularly machine learning, provides the capability to analyze vast quantities of data, identify patterns, and detect anomalies that might indicate an insider threat.
Leveraging Machine Learning for Behavioral Analytics
At the core of AI-driven insider threat detection is behavioral analytics. AI algorithms are trained on historical data sets of normal user behavior, learning baselines for activities such as login times, access patterns, data downloads, email usage, and network traffic. Once these baselines are established, any significant deviation from a user’s typical behavior, or from the behavior of their peer group, can trigger an alert. For instance, an employee who suddenly starts accessing highly sensitive files outside their usual working hours or forwarding large volumes of data to personal email accounts would be flagged for review.
Anomaly Detection and Risk Scoring
AI excels at anomaly detection, which is crucial for identifying insider threats. Instead of relying on a rigid set of rules, AI models learn what “normal” looks like and then pinpoint activities that deviate from that norm. This can include:
- Unusual data access patterns (e.g., accessing files outside one’s job role).
- Uncharacteristic network activity (e.g., attempting to connect to unauthorized external servers).
- Sudden changes in device usage (e.g., plugging in untrusted external drives).
- Attempts to bypass security controls or disable logging.
These anomalies are then often correlated and assigned a risk score. A single anomalous event might not be a significant concern, but a combination of several low-scoring anomalies could indicate a high-risk situation, prompting further investigation.
Addressing Privacy Concerns in AI-Driven Detection
The deployment of AI for insider threat detection, while beneficial for security, inherently raises significant privacy concerns. Comprehensive monitoring of employee activities can be perceived as an invasion of privacy, eroding trust and potentially leading to a hostile work environment. Navigating this fine line requires a well-considered approach that balances security imperatives with respect for individual rights.
Data Minimization and Purpose Limitation
A fundamental principle in mitigating privacy risks is data minimization. Organizations should only collect and process data that is strictly necessary for insider threat detection. This means avoiding the indiscriminate collection of all employee communications or personal web browsing history. Furthermore, the collected data must be used for its stated purpose only (purpose limitation) and not for unrelated surveillance or performance monitoring. Clearly defining the scope of data collection and its intended use is paramount.
Anonymization and Pseudonymization Techniques
To reduce the direct link between data and individual employees, organizations can employ anonymization and pseudonymization techniques. Anonymization aims to remove all identifiable information from data, making it impossible to re-identify an individual. Pseudonymization replaces direct identifiers with artificial identifiers, allowing for analysis without directly linking to a specific person, while retaining the ability to re-identify if necessary and under strict conditions. These techniques are particularly useful when training AI models or conducting aggregate analysis, where individual identity is not crucial.
Transparency and Employee Consent
Openness and communication are vital. Employees should be fully informed about the types of data being collected, the reasons for its collection, and how it will be used for insider threat detection. This transparency fosters trust and helps employees understand the necessity of such measures. While explicit consent for some monitoring activities might be difficult in an employment context, clear policies, readily accessible privacy notices, and opportunities for employees to ask questions contribute significantly to a more acceptable environment. Organizations should also provide clear channels for redress if an employee believes their privacy rights have been violated.
Legal and Ethical Frameworks
The implementation of AI for insider threat detection must operate within established legal and ethical boundaries. Ignoring these frameworks not only exposes organizations to legal penalties but also damages their reputation and employee morale.
Compliance with Data Protection Regulations
Organizations must adhere to relevant data protection regulations, such as the General Data Protection Regulation (GDPR) in Europe, the California Consumer Privacy Act (CCPA) in the United States, and similar legislation globally. These laws often dictate principles of lawful processing, data minimization, transparency, individual rights (e.g., right to access, right to erasure), and accountability. Failure to comply can result in substantial fines and legal challenges.
Establishing Clear Policies and Procedures
Robust internal policies and procedures are essential. These should clearly articulate:
- The scope and purpose of AI-driven monitoring.
- The types of data collected and how it is stored and secured.
- The criteria for triggering alerts and initiating investigations.
- The roles and responsibilities of personnel involved in the process.
- Employee rights and channels for complaints or appeals.
These policies should be regularly reviewed, updated, and communicated to all employees. A clear policy serves as a guide for both the organization and its employees, setting expectations and reducing ambiguity.
The Ethical Considerations of Employee Monitoring
Beyond legal compliance, ethical considerations play a crucial role. Organizations should strive for a “privacy-by-design” approach, integrating privacy protections into the very architecture of their AI systems. This includes minimizing the potential for bias in AI algorithms, as biased data sets can lead to unfair or discriminatory outcomes. Human oversight of AI-generated alerts is also critical. AI should act as a sophisticated filter, flagging potential risks for human analysts to investigate, rather than making autonomous decisions that could impact an employee’s employment status based solely on algorithmic output. The goal is to provide a safety net, not a surveillance state, for your workforce.
Best Practices for Implementation and Management
Successfully deploying AI for insider threat detection while respecting privacy requires a holistic approach that combines technological solutions with sound governance and human judgment.
Phased Implementation and Continuous Review
Instead of a “big bang” deployment, consider a phased implementation. Start with a pilot program in a controlled environment, perhaps with a small, representative group of users, to refine the system and identify potential issues. Continuous monitoring and review of the AI system’s performance, as well as its impact on employee privacy, are essential. As threat landscapes evolve and legal frameworks change, adjustments to the system and policies will be necessary. This iterative approach allows you to fine-tune your ‘fishing net’ to catch the ‘threat fish’ without ensnaring innocent ’employee fish’.
Integration with Existing Security Infrastructure
AI-driven insider threat detection tools should not operate in isolation. They should integrate seamlessly with existing security information and event management (SIEM) systems, identity and access management (IAM) solutions, and other security tools. This integrated approach allows for a more comprehensive view of an organization’s security posture and facilitates faster, more informed responses to potential threats. Think of it as adding a new, powerful sensor to your existing security ‘dashboard’, providing more data points for a holistic view.
Training and Awareness Programs
Technology alone is insufficient. Employees, especially those responsible for security operations and HR, need comprehensive training on the AI system, its capabilities, its limitations, and the associated privacy protocols. Regular awareness programs for all employees can also help educate them about insider threat risks and the importance of secure practices. When employees understand the ‘why’ behind the monitoring, they are more likely to accept it and even contribute to a stronger security culture. Equip your employees with knowledge, so they understand the ‘rulebook’ rather than feeling constantly under watch.
FAQs
What is insider threat detection?
Insider threat detection refers to the process of identifying and mitigating potential risks posed by individuals within an organization who have access to sensitive information and may misuse it for malicious purposes.
How does AI help in detecting insider threats?
AI can help in detecting insider threats by analyzing patterns of behavior, monitoring network activity, and identifying anomalies that may indicate potential security breaches or unauthorized access to sensitive data.
What are privacy rights and how are they relevant to insider threat detection?
Privacy rights refer to the legal rights of individuals to control their personal information and how it is used. In the context of insider threat detection, privacy rights are relevant because organizations must balance the need to protect sensitive data with the rights of employees to privacy.
How can AI detect insider threats without violating privacy rights?
AI can detect insider threats without violating privacy rights by using techniques such as anonymization, encryption, and access controls to ensure that sensitive data is protected while still allowing for the detection of potential security risks.
What are some best practices for implementing AI-based insider threat detection while respecting privacy rights?
Some best practices for implementing AI-based insider threat detection while respecting privacy rights include conducting privacy impact assessments, obtaining consent from employees, and implementing transparent and accountable data processing practices.