Unveiling the Threat: Understanding Adversarial Attacks on Machine Learning Models
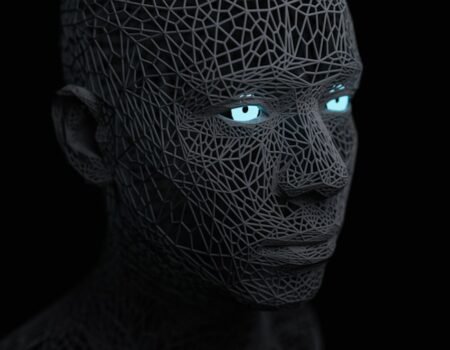
Introduction to Adversarial Machine Learning Machine learning models, despite...
The Key to Keeping Your Data Safe: Secure Prompt Engineering in LLM Deployments
This article discusses secure prompt engineering, a critical aspect of...
Protecting Your Identity: The Ultimate Guide to Defending Against Deepfake Attacks
Deepfakes, a portmanteau of “deep learning” and “fake,”...
Cracking the Code: Understanding How Generative Models are Fueling AI-Powered Phishing Attacks
The Evolving Landscape of Deception: Generative Models and AI-Powered Phishing...
Stay Ahead of Network Issues with NetCrunch: Real-Time Monitoring and Customizable Maps
In today’s rapidly evolving and interconnected digital landscape, the...
SMS Phishing (Smishing) 101: What You Need to Know to Stay Safe Online
SMS phishing, also referred to as smishing, is a form of cyber attack in which...
The Sneaky Art of Website Spoofing: What You Need to Know
Website spoofing is a malicious tactic employed by individuals or groups to...
The Sneaky Threat of Mobile Phishing: What You Need to Know
Mobile phishing is a rapidly escalating threat that poses significant risks to...
How does website spoofing work?
Website spoofing is a type of cyberattack in which a malicious actor creates a...
Protecting Your Sensitive Data: Understanding the Dangers of Unauthorized Access
In the digital era, safeguarding sensitive data has become a paramount concern....