Mitigating Risks: Best Practices for Implementing AI in Critical Infrastructure
This article outlines best practices for integrating artificial intelligence...
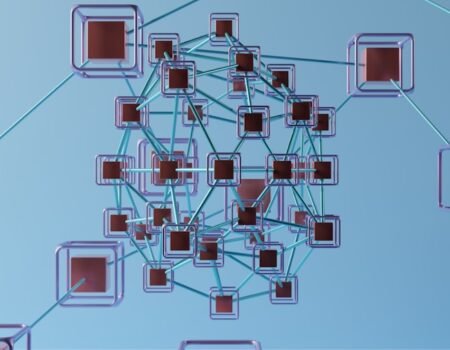
Revolutionizing Troubleshooting: The Impact of ML-Based Correlation on Telemetry Data
The troubleshooting of complex systems, from IT infrastructure to industrial...
Safeguarding Your AI Model APIs: Best Practices for Access Control and Security
Accessing artificial intelligence (AI) models through application programming...
Accelerating Vulnerability Discovery with AI-Assisted Fuzzing: A Game-Changer for Cybersecurity
The process of finding vulnerabilities in software systems has historically...
Protecting AI from Tampering: The Power of Model Provenance and Lineage Tracking
AI models, like any sophisticated tool, are susceptible to alteration. This...
Cracking the Code: How Model Provenance and Lineage Tracking Protect Against AI Tampering
The increasing integration of artificial intelligence (AI) systems across...
Revolutionizing Incident Response with AI Orchestration for Automated Playbooks
Artificial intelligence (AI) is increasingly being integrated into incident...
Unleashing the Power of AI: The Future of Automated Exploit Generation and PoC Crafting
The landscape of cybersecurity is in constant flux, a dynamic battlefield where...
Building Trust in Threat Intelligence Sharing: The Key to Privacy Protection
Threat intelligence sharing is a crucial component of modern cybersecurity...
AI and Ransomware: The Future of Cybercrime
The intersection of artificial intelligence (AI) and ransomware represents a...