Recent Posts
Safeguarding Your Production Systems: How to Detect and Prevent Prompt-Injection Attacks
January 27, 2026
Introduction to Prompt Injection Large Language Models (LLMs) have become integral to various production...
Mitigating Risks: Best Practices for Implementing AI in Critical Infrastructure
January 26, 2026
This article outlines best practices for integrating artificial intelligence (AI) into critical...
Revolutionizing Troubleshooting: The Impact of ML-Based Correlation on Telemetry Data
January 26, 2026
The troubleshooting of complex systems, from IT infrastructure to industrial control networks, has...
Safeguarding Your AI Model APIs: Best Practices for Access Control and Security
January 26, 2026
Accessing artificial intelligence (AI) models through application programming interfaces (APIs) has...
Accelerating Vulnerability Discovery with AI-Assisted Fuzzing: A Game-Changer for Cybersecurity
January 26, 2026
The process of finding vulnerabilities in software systems has historically been a painstaking endeavor....
Cracking the Code: How Model Provenance and Lineage Tracking Protect Against AI Tampering
January 25, 2026
The increasing integration of artificial intelligence (AI) systems across diverse sectors necessitates...
Protecting AI from Tampering: The Power of Model Provenance and Lineage Tracking
January 25, 2026
AI models, like any sophisticated tool, are susceptible to alteration. This alteration can manifest in...
Revolutionizing Incident Response with AI Orchestration for Automated Playbooks
January 25, 2026
Artificial intelligence (AI) is increasingly being integrated into incident response (IR) processes,...
Unleashing the Power of AI: The Future of Automated Exploit Generation and PoC Crafting
January 25, 2026
The landscape of cybersecurity is in constant flux, a dynamic battlefield where defenders strive to...
Building Trust in Threat Intelligence Sharing: The Key to Privacy Protection
January 25, 2026
Threat intelligence sharing is a crucial component of modern cybersecurity defense. Its effectiveness,...
AI and Ransomware: The Future of Cybercrime
January 24, 2026
The intersection of artificial intelligence (AI) and ransomware represents a significant and evolving...
Reducing False Positives: How Behavioural Analytics Enhances Insider Threat Detection
January 24, 2026
Insider threats represent a significant and evolving challenge for organizations across all sectors....
Level Up Your Red Team’s Phishing Tactics with LLMs: Creating Convincing Simulations
January 24, 2026
This article outlines how Large Language Models (LLMs) can be integrated into Red Team operations to...
Protecting Your Multi-Modal Model: Best Practices for Securing Text, Image, and Audio Processing
January 24, 2026
The rise of multi-modal models, capable of processing and generating content across text, images, and...
Defending Against Threats: Securing Multi-Modal Models for Text, Image, and Audio Processing
January 24, 2026
The increasing deployment of multi-modal models, capable of processing and generating information across...
Trending Articles
What are some best practices for businesses to improve cyber security?
December 20, 2020
One of the best practices for businesses to improve cyber security is to implement strong password...
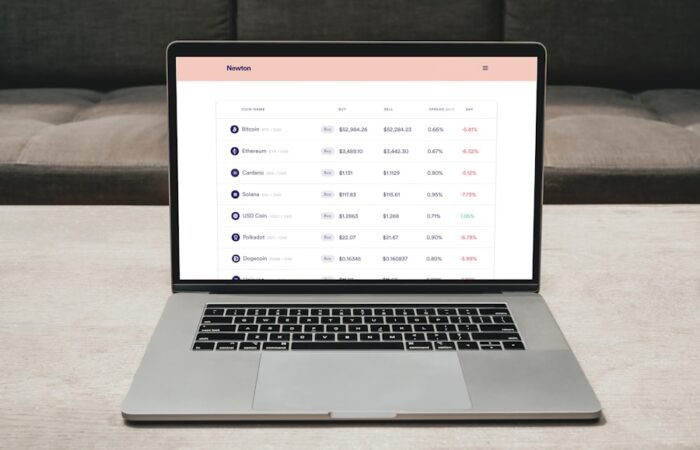
Bulletproofing Your Digital Wallet: Top Tips for Cryptocurrency Security
April 23, 2021
Cryptocurrency security is a vital component of digital asset ownership and management. As the...
From Code to Chaos: The Rise of AI-Generated Malware
January 21, 2026
From Code to Chaos: The Rise of AI-Generated Malware In the evolving landscape of cybersecurity, a new...
The Power of Anti-CSRF Tokens: Safeguarding Your Online Transactions
January 25, 2025
Anti-CSRF tokens, also referred to as Cross-Site Request Forgery tokens, play a vital role in securing...
What are some common cyber threats?
March 2, 2020
In the modern digital landscape, cyber threats have become increasingly frequent and complex....
Navigating the Ethical Landscape: AI Controls in Offensive Security
February 10, 2026
This article examines the integration of Artificial Intelligence (AI) within offensive security...
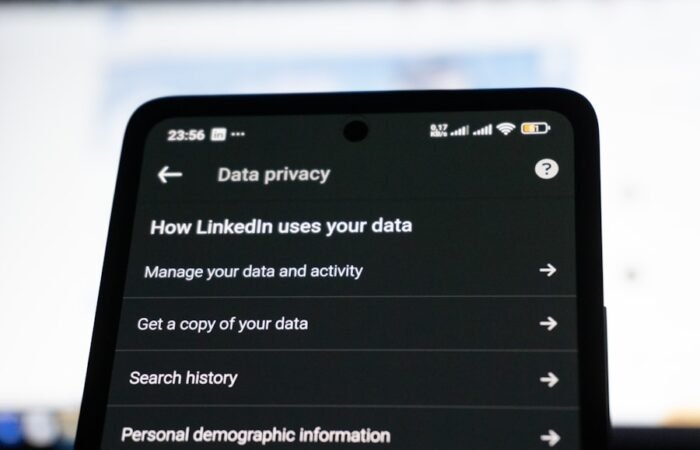
The Importance of Social Media Security: How to Keep Your Identity Safe Online
March 12, 2021
Social media has become an essential aspect of modern life, enabling users to connect with others, share...
The Key to Keeping Your Data Safe: Secure Prompt Engineering in LLM Deployments
January 21, 2026
This article discusses secure prompt engineering, a critical aspect of deploying Large Language Models...
Defending Against Data Poisoning: Securing Your Labeling Workflow from Malicious Actors
February 1, 2026
This article outlines strategies and considerations for defending against data poisoning attacks within...
Editor's Choice
Unlocking the Secrets of Unicornscan: A Deep Dive into Information Gathering and Port Scanning
June 17, 2023
Unicornscan is a robust information gathering and port scanning utility extensively utilized in the...
Navigating the Fine Line: How AI Can Detect Insider Threats Without Violating Privacy Rights
January 30, 2026
Understanding the Insider Threat Landscape Insider threats represent a significant vulnerability for...
How to Create a Cyber Security Awareness Program in Your Workplace
January 1, 2020
In today’s digitally driven landscape, cyber security awareness is vital for businesses that rely...
The Battle Against Adversarial AI: Strengthening Your OT/ICS Defenses
January 22, 2026
The integration of artificial intelligence (AI) and machine learning (ML) into operational technology...
Protecting Your Home and Business: The Growing Threat of IoT Security Vulnerabilities
February 16, 2025
In the modern digital era, the Internet of Things (IoT) has become a ubiquitous aspect of daily life,...
Maximizing Security and Control with Squid Proxy Server: A Comprehensive Guide
May 13, 2024
In the modern digital landscape, the significance of security and control in network management cannot...
Harnessing the Potential of Synthetic Threat Intelligence to Stay Ahead of Cyber Threats
January 22, 2026
Understanding Synthetic Threat Intelligence Synthetic threat intelligence (STI) represents a paradigm...
Navigating the Dark Web: Understanding the Risks and Threats
September 18, 2021
The dark web is a segment of the internet that remains inaccessible to traditional search engines and...
The Sneaky Ways Cybercriminals Target Your Phone: Common Mobile Phishing Techniques
February 15, 2025
Cybercriminals employ SMS phishing, also referred to as smishing, to deceive individuals into divulging...
Most Searched Topics
The Ultimate Guide to Cyber Security: What You Need to Know
January 10, 2020
Cybersecurity is the practice of safeguarding systems, networks, and programs from digital attacks....
Why is cyber security important?
September 11, 2020
In today’s digitally driven world, cyber security assumes paramount importance as it serves as the...
What are some common cyber threats?
March 2, 2020
In the modern digital landscape, cyber threats have become increasingly frequent and complex....
How can individuals protect themselves from cyber threats?
October 17, 2020
In the modern digital landscape, the significance of robust passwords and two-factor authentication...
What are some best practices for businesses to improve cyber security?
December 20, 2020
One of the best practices for businesses to improve cyber security is to implement strong password...
What is the role of government in cyber security?
October 4, 2020
The role of government in cyber security is crucial in today’s digital age. With the increasing...
What is a cyber security awareness program?
January 20, 2020
A cyber security awareness program is a comprehensive initiative that educates individuals on the...
Who should participate in a cyber security awareness program?
August 24, 2021
Participation in a cyber security awareness program is essential for employees at all levels within an...
Why is a cyber security awareness program important in the workplace?
March 25, 2021
In today’s digitally driven era, the risk of cyber attacks has reached unprecedented levels. With...
Cyber Security Tools and Softwares
Products not found
Empowering Your Digital Defence, One Click at a Time
Welcome to InfoSecArmy.com – Your Ultimate Cyber Security Resource
At InfoSecArmy.com, we are dedicated to empowering individuals and organisations with the knowledge and tools needed to navigate the complex landscape of Cyber Security. As the author of this blog site, I, Pramod Rimal, have immersed myself in various project-specific Cyber Security courses and bootcamp projects, equipping me with the expertise to guide you through this critical domain.
What We Offer:
Cyber Security Awareness: Stay informed about the latest trends and threats in the Cyber Security realm. Learn how to protect yourself and your digital assets from potential risks.
Do’s and Don’ts in Online Security: Explore essential guidelines on best practices for online security. Understand common pitfalls to avoid falling victim to cyber threats.
Safeguard Your Online Identity: Discover strategies to safeguard your online identity and personal information. Learn how to protect your privacy in the digital world.
Cyber Security Tools: Dive into the world of tools used to identify and mitigate cybersecurity threats. Understand the advantages and disadvantages of these tools and how to leverage them effectively.
Choosing the Right Tools: Gain insights into selecting the most suitable Cyber Security tools for your specific needs. Learn how to evaluate tools based on their functionalities and how they align with your security objectives.
Additional Key Focus Areas:
Incident Response Planning: Develop strategies to effectively respond to cybersecurity incidents. Learn how to mitigate risks and minimise the impact of potential breaches.
Regulatory Compliance: Stay abreast of the latest regulations and standards in Cyber Security. Understand the compliance requirements relevant to your industry or organisation.
Best Practices in Cyber Security: Access a wealth of knowledge on industry best practices, from secure coding principles to network security measures. Enhance your cyber resilience through expert guidance.
Threat Intelligence: Harness the power of threat intelligence to proactively identify and counter cyber threats. Stay one step ahead of potential attackers with timely insights.
Stay Updated with Trending News:
Our blog site is dedicated to delivering current trending news and articles related to Cyber Security. Stay informed about emerging threats, innovative technologies, and industry developments that impact the cyber landscape.
Join us at InfoSecArmy.com as we embark on a journey to fortify our digital defences, raise awareness about Cyber Security, and empower individuals and organisations to navigate the ever-evolving cyber threat landscape. Together, we can build a safer, more secure digital world.

Pramod Rimal
Author/Writer Full Stack Digital Marketer