Reducing False Positives: How Behavioural Analytics Enhances Insider Threat Detection
Insider threats represent a significant and evolving challenge for...
Level Up Your Red Team’s Phishing Tactics with LLMs: Creating Convincing Simulations
This article outlines how Large Language Models (LLMs) can be integrated into...
Protecting Your Multi-Modal Model: Best Practices for Securing Text, Image, and Audio Processing
The rise of multi-modal models, capable of processing and generating content...
Defending Against Threats: Securing Multi-Modal Models for Text, Image, and Audio Processing
The increasing deployment of multi-modal models, capable of processing and...
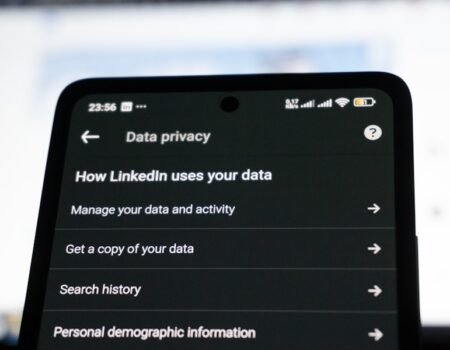
Protecting Your Privacy in the Age of AI: What You Need to Know About Data Exfiltration
Introduction The pervasive integration of Artificial Intelligence (AI) into...
From Chaos to Clarity: The Impact of ML Confidence Scoring on Incident Management
Introduction to Incident Management Challenges Incident management, at its...
Unleashing the Power of Machine Learning: Detecting Intruders in Your Network
In the contemporary digital landscape, networks serve as the circulatory system...
Defending Against the Unseen: Bolstering Endpoint Security Against AI-Crafted Polymorphic Malware
As a Wikipedia editor, I present an article on the subject you requested. The...
The Battle Against Adversarial AI: Strengthening Your OT/ICS Defenses
The integration of artificial intelligence (AI) and machine learning (ML) into...
Empowering Security Teams: Leveraging AI-Driven Anomaly Detection for Early Threat Identification
The increasing complexity and volume of cyber threats present a significant...