Recent Posts
Unleashing the Power of Offensive AI in Security Testing: Ethical Guidelines to Consider
February 3, 2026
Modern cybersecurity faces a complex landscape, requiring innovative approaches to security testing. One...
The Future of Post-Exploitation Automation: Leveraging AI for Persistent Access and Data Exfiltration
February 3, 2026
The integration of artificial intelligence (AI) into cybersecurity, particularly within the realm of...
The Essential Guide to Vendor Assessment and Contractual Safeguards for Third-Party AI
February 2, 2026
When your organization integrates Artificial Intelligence (AI) through third-party vendors, you are...
Stay Ahead of the Game: Using AI to Secure Your Cloud Workloads from Configuration Drift
February 2, 2026
The following content is presented as an informational article. This article discusses the use of...
The Art of Ethical Hacking: Automating Credential-Stuffing and Password Spray Campaigns for Assessment
February 2, 2026
The article “The Art of Ethical Hacking: Automating Credential-Stuffing and Password Spray...
Unveiling the Power of AI-Enhanced Honeytokens and Honeypots: The Ultimate Deception Techniques
February 2, 2026
Artificial intelligence (AI) is transforming cybersecurity, particularly in defensive strategies like...
Defending Against Data Poisoning: Securing Your Labeling Workflow from Malicious Actors
February 1, 2026
This article outlines strategies and considerations for defending against data poisoning attacks within...
Harnessing the Power of AI: Automated Data Exfiltration Detection and Blocking with Pattern-Learning Models
February 1, 2026
Data exfiltration, the unauthorized transfer of data from a computer or network, represents a...
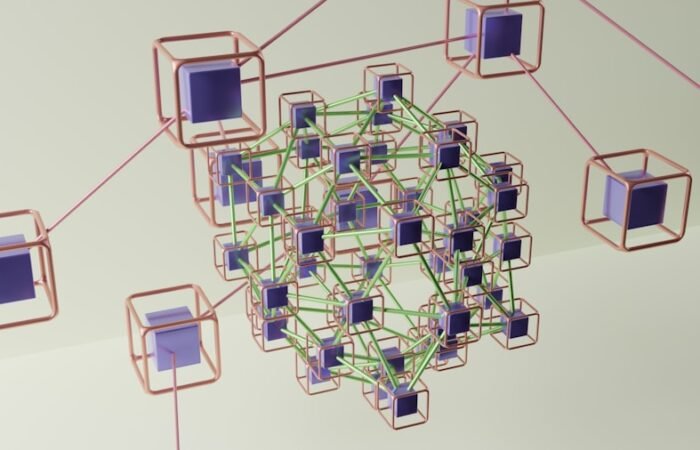
Securing Networks with Graph Neural Networks: Identifying Vulnerable Nodes
February 1, 2026
Your exploration of network security in the digital age will invariably lead you to the challenges of...
Putting Models to the Test: How to Measure Adversarial Resistance
February 1, 2026
Understanding Adversarial Resistance in Models The development of machine learning models, particularly...
Cracking the Code: Legal and Compliance Considerations in Investigating AI-Related Cyber Incidents
January 31, 2026
The integration of Artificial Intelligence (AI) into critical infrastructure and business operations...
The Future of Cybersecurity: AI-Enabled Malware Sandboxing and Behaviour Fingerprint Clustering
January 31, 2026
The evolving landscape of cyber threats necessitates advanced defense mechanisms. Traditional...
AI-Powered Pentesting: Streamlining Business Risk and Exploitability Prioritization
January 31, 2026
This article discusses the application of artificial intelligence (AI) in penetration testing, focusing...
Revolutionizing Cybersecurity: AI’s Role in Automating Patch Prioritization
January 31, 2026
Introduction The landscape of cybersecurity is continuously evolving, with new vulnerabilities and...
Navigating the Fine Line: How AI Can Detect Insider Threats Without Violating Privacy Rights
January 30, 2026
Understanding the Insider Threat Landscape Insider threats represent a significant vulnerability for...
Trending Articles
How can individuals protect themselves from cyber threats?
October 17, 2020
In the modern digital landscape, the significance of robust passwords and two-factor authentication...
The Key to Keeping Your Data Safe: Secure Prompt Engineering in LLM Deployments
January 21, 2026
This article discusses secure prompt engineering, a critical aspect of deploying Large Language Models...
Outsmarting AI-Driven Lateral Movement: Enhancing Your Zero-Trust Defenses
January 21, 2026
The proliferation of artificial intelligence (AI) in cybersecurity presents both advancements in...
Stay Ahead of Cyber Threats with Snort: The Ultimate Intrusion Detection System
November 4, 2020
In the modern digital landscape, cybersecurity has become a paramount concern for individuals,...
Honeypots: The Secret Weapon in Your Cybersecurity Arsenal
January 23, 2024
In the world of cybersecurity, honeypots are a powerful and often underutilized tool for detecting and...
What are some common cyber threats?
March 2, 2020
In the modern digital landscape, cyber threats have become increasingly frequent and complex....
Mastering Metasploit: A Beginner’s Guide to Exploiting Vulnerabilities
October 22, 2021
Metasploit is a robust penetration testing framework extensively utilized by security professionals and...
The Art of Ethical Hacking: Automating Credential-Stuffing and Password Spray Campaigns for Assessment
February 2, 2026
The article “The Art of Ethical Hacking: Automating Credential-Stuffing and Password Spray...
Mastering Metasploit: The Ultimate Cybersecurity Tool
February 26, 2021
Metasploit is a potent open-source cybersecurity framework widely utilized by security professionals and...
Editor's Choice
Revolutionizing Troubleshooting: The Impact of ML-Based Correlation on Telemetry Data
January 26, 2026
The troubleshooting of complex systems, from IT infrastructure to industrial control networks, has...
How to Harness the Full Potential of ELK Stack for Data Analysis
February 7, 2025
The ELK Stack is a potent combination of three open-source tools: Elasticsearch, Logstash, and Kibana....
The Art of Red Teaming LLMs: Strategies for Ensuring AI Robustness and Security
January 21, 2026
The proliferation of large language models (LLMs) has introduced both unprecedented capabilities and...
What are the potential legal consequences of using Aircrack-ng unlawfully?
May 20, 2020
Aircrack-ng is a widely utilized network software suite employed for penetration testing and network...
The Ultimate Guide to Using MISP for Effective Malware Information Sharing
January 10, 2025
Malware information sharing is a vital component of cybersecurity, enabling organizations to stay ahead...
From Code to Chaos: The Rise of AI-Generated Malware
January 21, 2026
From Code to Chaos: The Rise of AI-Generated Malware In the evolving landscape of cybersecurity, a new...
Protecting Your Company from Within: Strategies for Managing Insider Threats
January 19, 2025
Companies today face a significant risk from insider threats, which originate from individuals within...
Defusing the Threat: How to Detect and Prevent Logic Bombs from Damaging Your Systems
July 9, 2023
A logic bomb is a type of malicious software (malware) that is programmed to execute a predetermined set...
Inside the Mind of John the Ripper: The World’s Most Powerful Password Cracking Tool
January 28, 2025
John the Ripper is a highly effective and widely utilized password cracking tool with a history spanning...
Most Searched Topics
Osquery: The Ultimate Endpoint Security Tool You Need to Know About
November 23, 2020
Osquery is an open-source endpoint security tool that enables organizations to easily access and analyze...
Stay Ahead of Cyber Threats: Leveraging RSA NetWitness Network Traffic Analysis Tool for Proactive Defense
December 11, 2020
In the contemporary digital era, the cyber threat landscape is undergoing perpetual transformation, with...
The Ultimate Guide to Cyber Security: Keeping Your Digital Life Safe
February 13, 2020
In the modern digital era, cybersecurity has become a paramount concern. The growing reliance on digital...
The Ultimate Guide to Cyber Security: What You Need to Know
January 10, 2020
Cybersecurity is the practice of safeguarding systems, networks, and programs from digital attacks....
Why is cyber security important?
September 11, 2020
In today’s digitally driven world, cyber security assumes paramount importance as it serves as the...
What are some common cyber threats?
March 2, 2020
In the modern digital landscape, cyber threats have become increasingly frequent and complex....
How can individuals protect themselves from cyber threats?
October 17, 2020
In the modern digital landscape, the significance of robust passwords and two-factor authentication...
What are some best practices for businesses to improve cyber security?
December 20, 2020
One of the best practices for businesses to improve cyber security is to implement strong password...
What is the role of government in cyber security?
October 4, 2020
The role of government in cyber security is crucial in today’s digital age. With the increasing...
Cyber Security Tools and Softwares
Products not found
Empowering Your Digital Defence, One Click at a Time
Welcome to InfoSecArmy.com – Your Ultimate Cyber Security Resource
At InfoSecArmy.com, we are dedicated to empowering individuals and organisations with the knowledge and tools needed to navigate the complex landscape of Cyber Security. As the author of this blog site, I, Pramod Rimal, have immersed myself in various project-specific Cyber Security courses and bootcamp projects, equipping me with the expertise to guide you through this critical domain.
What We Offer:
Cyber Security Awareness: Stay informed about the latest trends and threats in the Cyber Security realm. Learn how to protect yourself and your digital assets from potential risks.
Do’s and Don’ts in Online Security: Explore essential guidelines on best practices for online security. Understand common pitfalls to avoid falling victim to cyber threats.
Safeguard Your Online Identity: Discover strategies to safeguard your online identity and personal information. Learn how to protect your privacy in the digital world.
Cyber Security Tools: Dive into the world of tools used to identify and mitigate cybersecurity threats. Understand the advantages and disadvantages of these tools and how to leverage them effectively.
Choosing the Right Tools: Gain insights into selecting the most suitable Cyber Security tools for your specific needs. Learn how to evaluate tools based on their functionalities and how they align with your security objectives.
Additional Key Focus Areas:
Incident Response Planning: Develop strategies to effectively respond to cybersecurity incidents. Learn how to mitigate risks and minimise the impact of potential breaches.
Regulatory Compliance: Stay abreast of the latest regulations and standards in Cyber Security. Understand the compliance requirements relevant to your industry or organisation.
Best Practices in Cyber Security: Access a wealth of knowledge on industry best practices, from secure coding principles to network security measures. Enhance your cyber resilience through expert guidance.
Threat Intelligence: Harness the power of threat intelligence to proactively identify and counter cyber threats. Stay one step ahead of potential attackers with timely insights.
Stay Updated with Trending News:
Our blog site is dedicated to delivering current trending news and articles related to Cyber Security. Stay informed about emerging threats, innovative technologies, and industry developments that impact the cyber landscape.
Join us at InfoSecArmy.com as we embark on a journey to fortify our digital defences, raise awareness about Cyber Security, and empower individuals and organisations to navigate the ever-evolving cyber threat landscape. Together, we can build a safer, more secure digital world.

Pramod Rimal
Author/Writer Full Stack Digital Marketer