Recent Posts
– Threat Attribution Assistance: Linking TTPs With Likely Actor Profiles Via ML
January 30, 2026
Imagine a digital battlefield where attackers leave behind a trail of breadcrumbs. These breadcrumbs,...
Navigating the Cyber Maze: How AI Predicts Attacker Paths in Enterprise Networks
January 30, 2026
The increasing complexity of enterprise networks presents significant challenges to cybersecurity....
Cracking the Code of Threat Hunting: How AI and Human Intuition Team Up to Stay Ahead of Cyber Attacks
January 30, 2026
The persistent and evolving nature of cyber threats necessitates proactive defense strategies. While...
The Future of Data Security: Exploring Cryptographic Solutions for Model Inference
January 29, 2026
The rapid advancement of artificial intelligence (AI) and machine learning (ML) has brought about...
Homomorphic Encryption: The Key to Secure Model Inference
January 29, 2026
Homomorphic encryption is a cryptographic technique that allows computation to be performed on encrypted...
From Chaos to Clarity: Using AI to Transform Noisy Feeds into Actionable Threat Intelligence
January 29, 2026
Here is an article about the topic, written in a factual style suitable for Wikipedia, without excessive...
Empowering Security Teams: Harnessing Reinforcement Learning for Autonomous Penetration Testing
January 29, 2026
This article explores the application of reinforcement learning (RL) to automate penetration testing,...
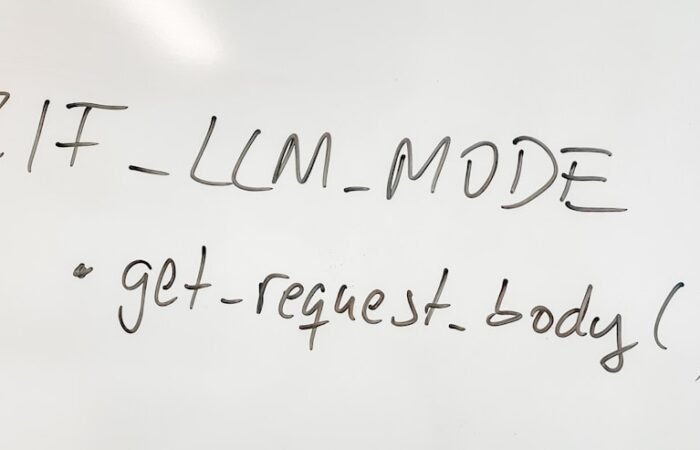
Mastering Secure Configuration Management for AI Platforms: Best Practices and Tips
January 29, 2026
Configuration management is a critical component for maintaining the integrity, security, and...
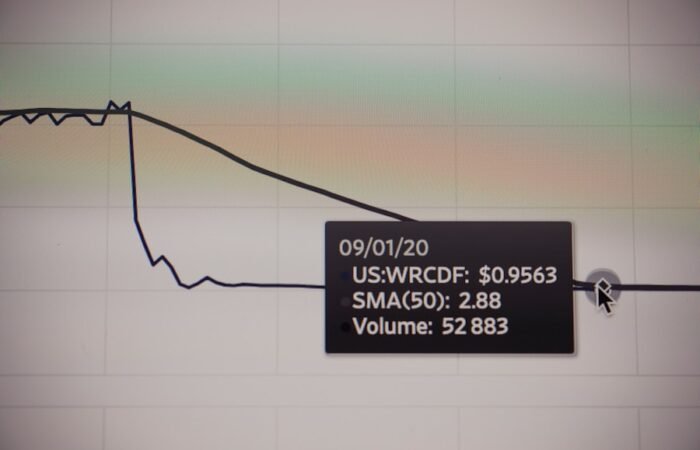
Protecting Your Data: Using Model Drift to Detect Compromises and Changes
January 28, 2026
As a data professional or system administrator, you understand that securing your data is paramount. In...
The Art of Adaptive Deception: How AI-Managed Honeynets are Changing the Game in Cybersecurity
January 28, 2026
The evolution of cybersecurity threats necessitates advanced defense mechanisms. Traditional security...
Mastering Intelligent Port and Service Discovery: Adapting Probing Strategies in Real Time
January 28, 2026
Understanding the Landscape: Foundations of Intelligent Port and Service Discovery Intelligent port and...
Securing On-Device AI: Best Practices for Safeguarding Models and Data on Mobile and Edge Devices
January 28, 2026
Mobile and edge devices are increasingly hosting sophisticated Artificial Intelligence (AI) models,...
Defending Your Chatbot: How to Protect Against Social Engineering Attacks
January 27, 2026
Chatbots, increasingly integrated into customer service, information dissemination, and even personal...
Protecting Your Assets: The Benefits of Real-Time AI Threat Exposure Scoring
January 27, 2026
Understanding Real-Time AI Threat Exposure Scoring Real-time AI threat exposure scoring represents a...
Stay Ahead of the Game: Defending Against Adversarial ML Evasion Tactics in IDS/IPS Systems
January 27, 2026
In the realm of cybersecurity, Intrusion Detection Systems (IDS) and Intrusion Prevention Systems (IPS)...
Trending Articles
What are the potential concerns with biometric security?
May 7, 2023
Biometric security systems, including fingerprint scanners and facial recognition technology, pose...
DevSecOps for AI: How to Integrate Security into the ML Lifecycle
January 21, 2026
The integration of security practices into the machine learning (ML) lifecycle, often termed DevSecOps...
The Ultimate Guide to Cyber Security: Keeping Your Digital Life Safe
February 13, 2020
In the modern digital era, cybersecurity has become a paramount concern. The growing reliance on digital...
Defending Against SQL Injection Attacks: Best Practices for Database Security
February 7, 2024
SQL injection attacks constitute a significant security threat to databases, as they involve the...
The Power of Realism: How Synthetic Network Environments Elevate Pentest Training
February 4, 2026
Pentesters, like any skilled professionals, require rigorous training to maintain and advance their...
Biometric Security: The Future of Authentication in Cyber Space
April 3, 2022
Biometric security is a state-of-the-art technology that is transforming the way we authenticate our...
Mastering Metasploit: The Ultimate Cybersecurity Tool
February 26, 2021
Metasploit is a potent open-source cybersecurity framework widely utilized by security professionals and...
The Art of Packet Sniffing: A Beginner’s Guide to Understanding Network Traffic
June 3, 2024
Packet sniffing is a network monitoring technique that involves intercepting and logging network...
Hydra: Your Secret Weapon for Breaking Through Password Security
August 10, 2020
In the realm of cybersecurity, password security is a vital aspect of safeguarding sensitive information...
Editor's Choice
Is Nmap Legal? Understanding the Legality of Network Scanning Tools
August 3, 2024
Nmap, or Network Mapper, is a widely utilized open-source tool for network exploration and security...
Forensic Considerations for Incident Response in AI Systems: Best Practices
January 21, 2026
This article outlines forensic considerations for incident response in artificial intelligence (AI)...
From Nodes to Networks: Exploring the Best Tools for Network Mapping
January 19, 2025
Network mapping is a potent tool employed to visualize and analyze complex systems by creating visual...
Balancing Privacy and Security: Leveraging Differential Privacy for Anomaly Detection
February 8, 2026
The challenge of protecting sensitive information while simultaneously extracting valuable insights is a...
Why is a cyber security awareness program important in the workplace?
March 25, 2021
In today’s digitally driven era, the risk of cyber attacks has reached unprecedented levels. With...
Cyber Security for Small Businesses: Importance and Implementation
April 3, 2022
In the modern digital landscape, cybersecurity has emerged as a paramount concern for businesses of all...
Harnessing the Power of AI: Automated Data Exfiltration Detection and Blocking with Pattern-Learning Models
February 1, 2026
Data exfiltration, the unauthorized transfer of data from a computer or network, represents a...
Maximizing Security: How Model-Based Prediction Can Prioritize Patching Schedules
February 4, 2026
In the digital realm, the challenge of maintaining robust security is a constant race against evolving...
Mastering Wireshark: How to Analyze Network Traffic Like a Pro
January 2, 2020
Wireshark is a robust network protocol analyzer that enables users to capture and interactively examine...
Most Searched Topics
The Ultimate Guide to Cyber Security: What You Need to Know
January 10, 2020
Cybersecurity is the practice of safeguarding systems, networks, and programs from digital attacks....
Why is cyber security important?
September 11, 2020
In today’s digitally driven world, cyber security assumes paramount importance as it serves as the...
What are some common cyber threats?
March 2, 2020
In the modern digital landscape, cyber threats have become increasingly frequent and complex....
How can individuals protect themselves from cyber threats?
October 17, 2020
In the modern digital landscape, the significance of robust passwords and two-factor authentication...
What are some best practices for businesses to improve cyber security?
December 20, 2020
One of the best practices for businesses to improve cyber security is to implement strong password...
What is the role of government in cyber security?
October 4, 2020
The role of government in cyber security is crucial in today’s digital age. With the increasing...
What is a cyber security awareness program?
January 20, 2020
A cyber security awareness program is a comprehensive initiative that educates individuals on the...
Who should participate in a cyber security awareness program?
August 24, 2021
Participation in a cyber security awareness program is essential for employees at all levels within an...
Why is a cyber security awareness program important in the workplace?
March 25, 2021
In today’s digitally driven era, the risk of cyber attacks has reached unprecedented levels. With...
Cyber Security Tools and Softwares
Products not found
Empowering Your Digital Defence, One Click at a Time
Welcome to InfoSecArmy.com – Your Ultimate Cyber Security Resource
At InfoSecArmy.com, we are dedicated to empowering individuals and organisations with the knowledge and tools needed to navigate the complex landscape of Cyber Security. As the author of this blog site, I, Pramod Rimal, have immersed myself in various project-specific Cyber Security courses and bootcamp projects, equipping me with the expertise to guide you through this critical domain.
What We Offer:
Cyber Security Awareness: Stay informed about the latest trends and threats in the Cyber Security realm. Learn how to protect yourself and your digital assets from potential risks.
Do’s and Don’ts in Online Security: Explore essential guidelines on best practices for online security. Understand common pitfalls to avoid falling victim to cyber threats.
Safeguard Your Online Identity: Discover strategies to safeguard your online identity and personal information. Learn how to protect your privacy in the digital world.
Cyber Security Tools: Dive into the world of tools used to identify and mitigate cybersecurity threats. Understand the advantages and disadvantages of these tools and how to leverage them effectively.
Choosing the Right Tools: Gain insights into selecting the most suitable Cyber Security tools for your specific needs. Learn how to evaluate tools based on their functionalities and how they align with your security objectives.
Additional Key Focus Areas:
Incident Response Planning: Develop strategies to effectively respond to cybersecurity incidents. Learn how to mitigate risks and minimise the impact of potential breaches.
Regulatory Compliance: Stay abreast of the latest regulations and standards in Cyber Security. Understand the compliance requirements relevant to your industry or organisation.
Best Practices in Cyber Security: Access a wealth of knowledge on industry best practices, from secure coding principles to network security measures. Enhance your cyber resilience through expert guidance.
Threat Intelligence: Harness the power of threat intelligence to proactively identify and counter cyber threats. Stay one step ahead of potential attackers with timely insights.
Stay Updated with Trending News:
Our blog site is dedicated to delivering current trending news and articles related to Cyber Security. Stay informed about emerging threats, innovative technologies, and industry developments that impact the cyber landscape.
Join us at InfoSecArmy.com as we embark on a journey to fortify our digital defences, raise awareness about Cyber Security, and empower individuals and organisations to navigate the ever-evolving cyber threat landscape. Together, we can build a safer, more secure digital world.

Pramod Rimal
Author/Writer Full Stack Digital Marketer